Python Code Tutorials
How to Use Python to Track Google Search Results and Reviews Over Time
Learn how to use Python to scrape Google search results and review ratings. Track changes over time to monitor SEO, online reputation, and competitor activity.
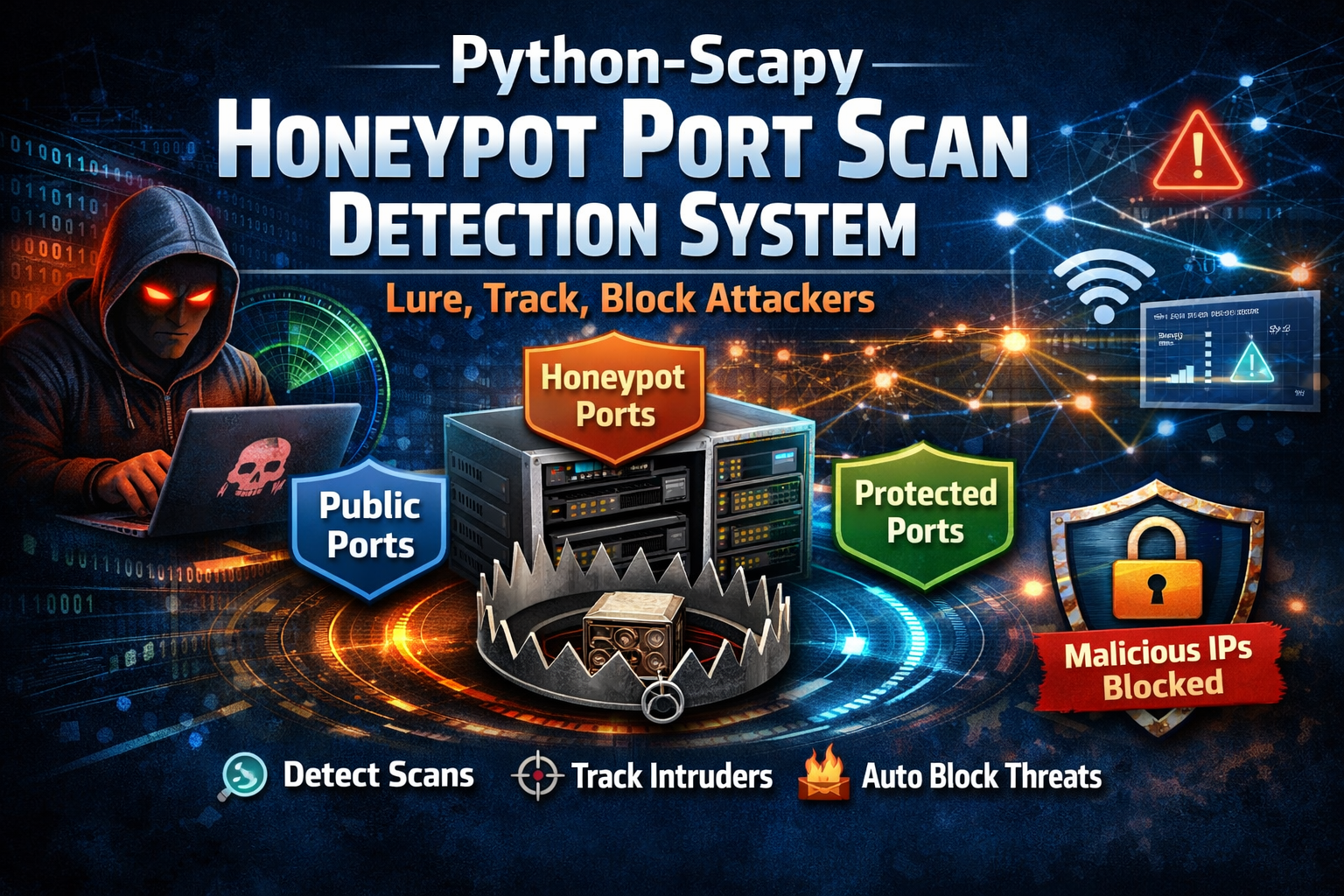
Building a Honeypot Defense System with Python and Scapy
Build a Python-based honeypot defense system with Scapy that detects port scanning, lures attackers using decoy ports, tracks reconnaissance activity, and automatically blocks malicious IPs.
Nearshore vs Offshore: Cost-Effective Software Development
Discover the key differences between nearshore and offshore software development. Learn which model offers the best balance of cost, quality, and collaboration for your project.

A Simple, Easy-to-Follow Guide to Python Coding on Apple-Based Machines
A quick guide to setting up Python on macOS, covering installation, tools (IDEs), virtual environments, learning resources, and basic best practices for a secure and efficient workflow.