Python Code Tutorials

How to Generate and Visualize Text Embeddings in Python
Learn how text embeddings work in Python using Sentence Transformers. Generate embeddings, compare semantic similarity, and visualize the embedding space with PCA, t-SNE, heatmaps, and dimension analysis.
How to Build a Semantic Search Engine with FAISS and Sentence Transformers in Python
Build a fully local semantic search engine in Python using FAISS and Sentence Transformers. Learn how embeddings work, index vectors, run semantic queries, and visualize the embedding space with PCA.
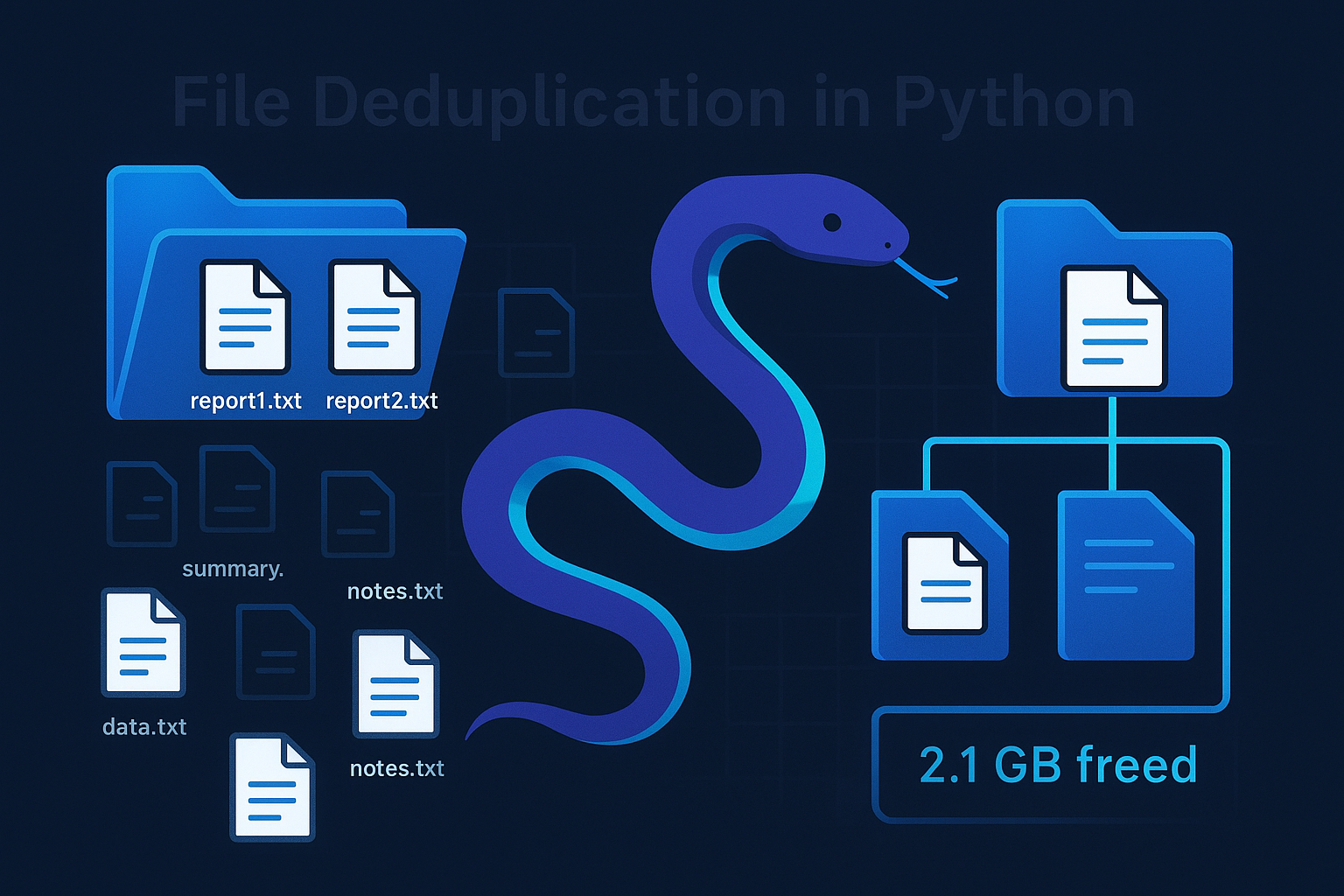
How to Build a File Deduplication Tool in Python
Learn how to build a Python tool that scans directories, finds duplicate files by SHA256 hash, and calculates reclaimable disk space. Features Rich progress bars, tables, and a clean CLI experience.

SQL Analytics at Lightning Speed: Getting Started with DuckDB in Python
Learn how to use DuckDB in Python for lightning-fast SQL analytics on CSV, Parquet, and JSON files. Covers installation, querying, hybrid Pandas/Polars workflows, and performance tips.

A Simple, Easy-to-Follow Guide to Python Coding on Apple-Based Machines
A quick guide to setting up Python on macOS, covering installation, tools (IDEs), virtual environments, learning resources, and basic best practices for a secure and efficient workflow.
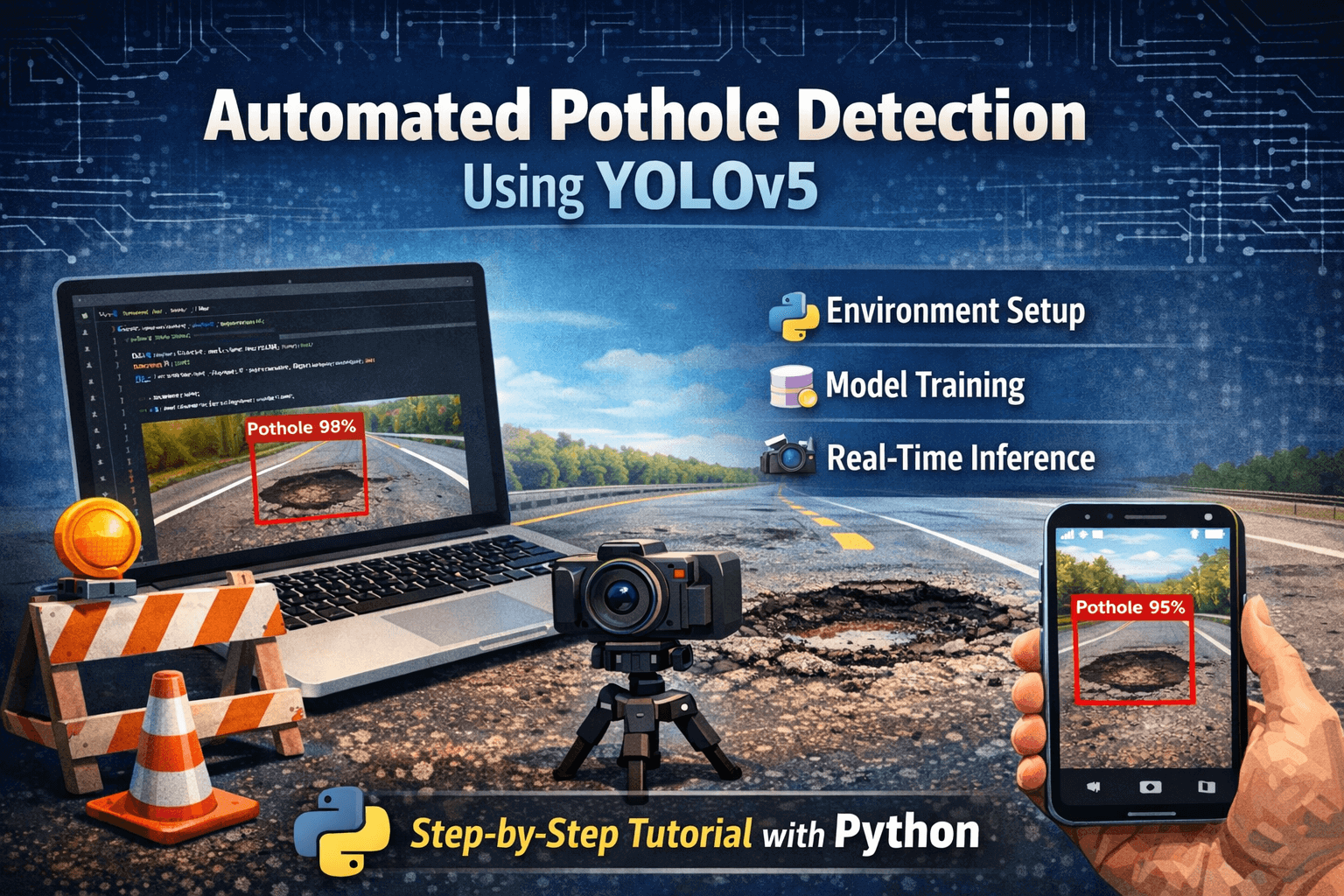
Automated Pothole Detection Using YOLO in Python
Learn how to build an automated pothole detection system using YOLOv5. This step-by-step tutorial covers environment setup, model training with a custom dataset, and running inference for real-time detection on images.
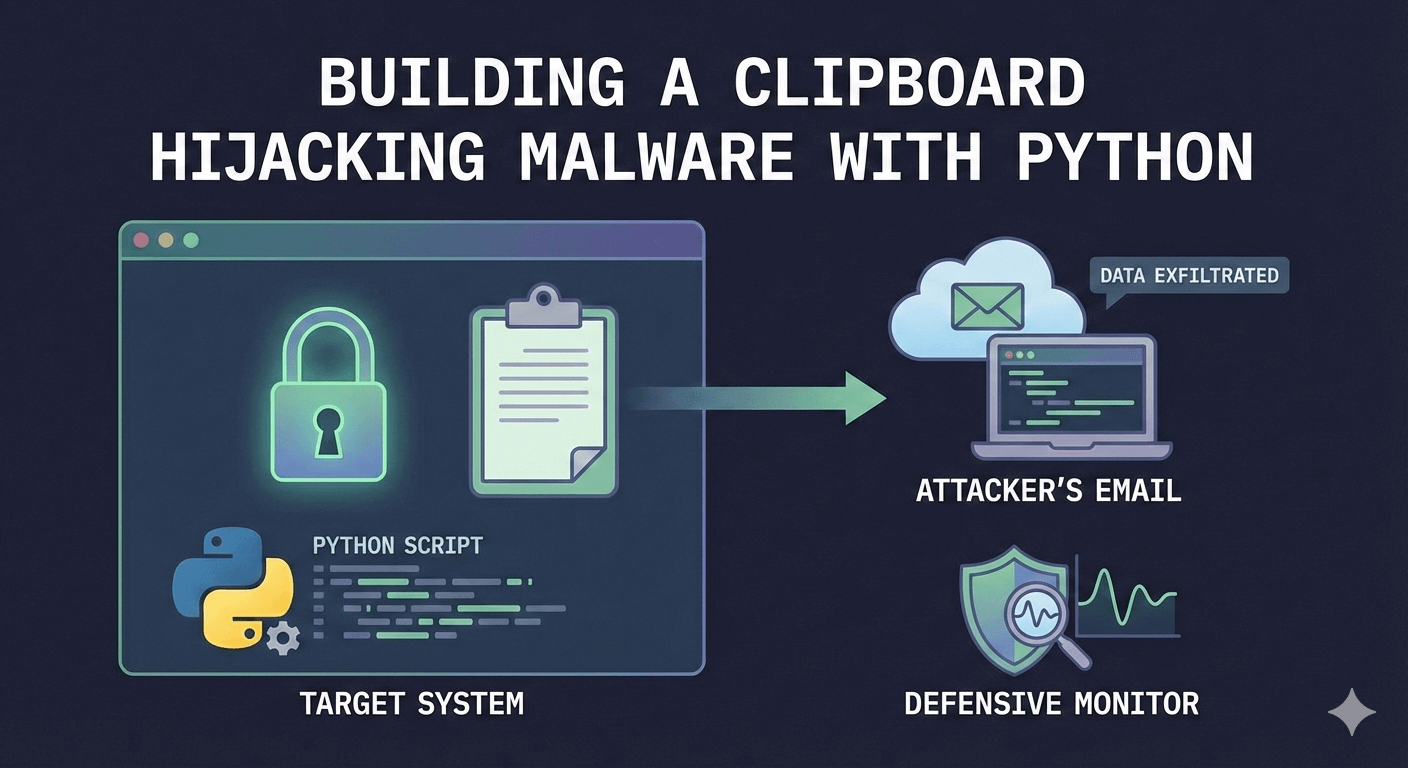
Building a ClipBoard Hijacking Malware with Python
Learn how to build a clipboard hijacking tool that monitors copied content, silently replaces email addresses and exfiltrates clipboard data from a target and sends to the attacker remotely via email. You'll also learn to build defensive monitor to detect unauthorized clipboard modifications on Windows and Linux
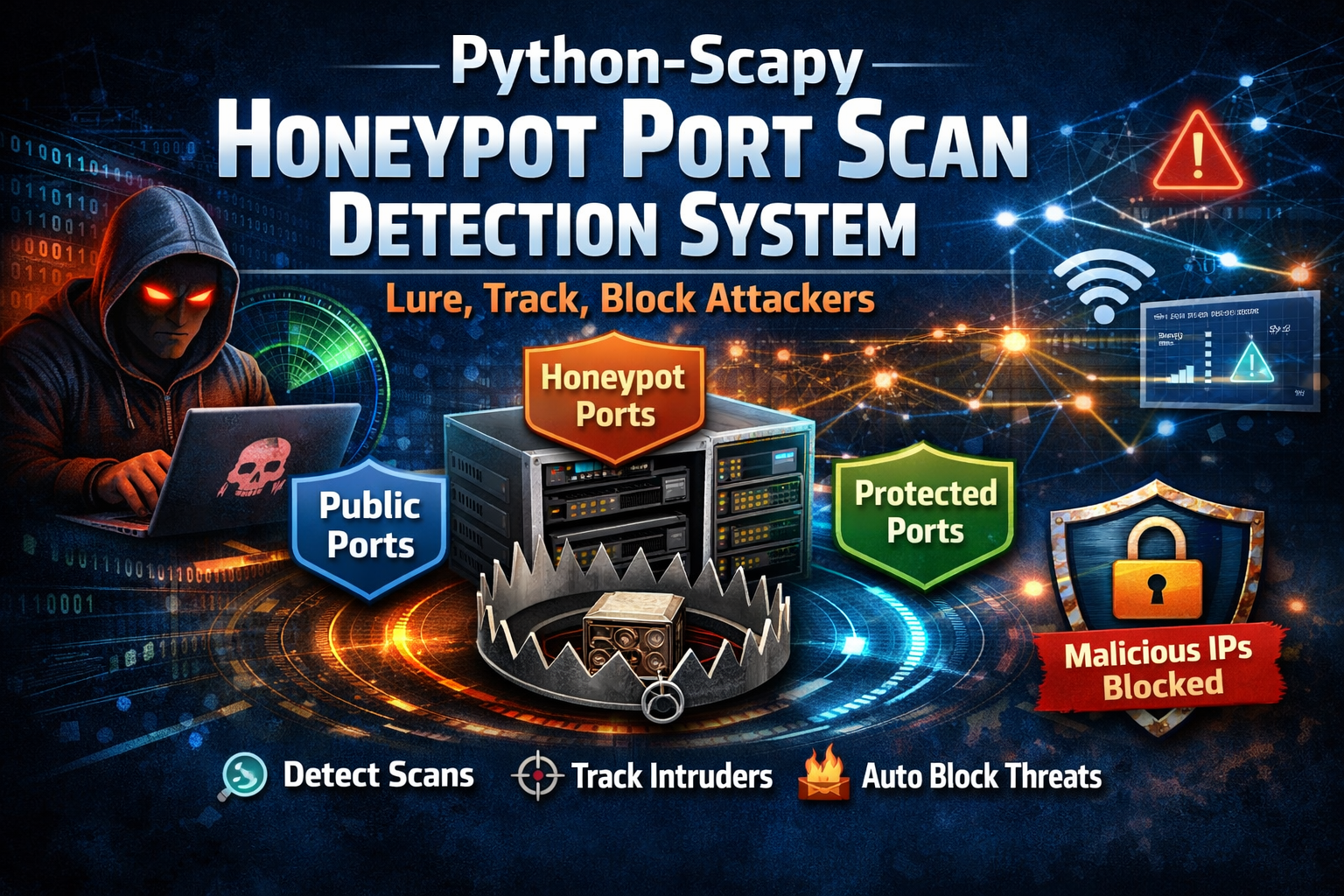
Building a Honeypot Defense System with Python and Scapy
Build a Python-based honeypot defense system with Scapy that detects port scanning, lures attackers using decoy ports, tracks reconnaissance activity, and automatically blocks malicious IPs.
Build an MCP Server in Python with FastMCP
Build a real MCP server and client in Python using FastMCP. Implement a Todo Manager with tools, resources, and prompts, test it programmatically, then wire it into Claude Desktop, VS Code, and Cursor. Includes simple production deployment tips.
Building an AI-Driven HTTP Security Headers Analyzer with Python
Build a Python tool that checks HTTP security headers and uses DeepSeek AI to provide practical insights, missing protections, and security recommendations.
Building an Advanced Audiobook Generator with Python and ElevenLabs TTS
Learn to create professional audiobooks in Python with ElevenLabs’ AI text-to-speech, covering setup, voice options, and full generation.
Building a Full-Stack RAG Chatbot with FastAPI, OpenAI, and Streamlit
Learn to build a full-stack RAG chatbot with FastAPI, OpenAI, and Streamlit. Step-by-step guide to create a chatbot answering questions from uploaded PDFs.
How to Recover Deleted Files with Python
Learn how to recover deleted files using Python by scanning raw disk data for known file signatures. This step-by-step guide walks you through creating a basic file carving tool to retrieve lost JPGs, PDFs, DOCX files, and more.
How to Use Python to Track Google Search Results and Reviews Over Time
Learn how to use Python to scrape Google search results and review ratings. Track changes over time to monitor SEO, online reputation, and competitor activity.
YouTube Video Transcription Summarization with Python
Learn how to transcribe and summarize YouTube videos using Python! This tutorial covers extracting video transcripts with YouTubeTranscriptApi, processing text with NLTK, and generating AI-powered summaries using OpenRouter's Mistral model.
Getting Started with Python for SaaS Applications
Learn how to build a SaaS application using Python in this comprehensive guide. From setting up your environment and choosing a framework to deploying on the cloud, this article covers everything you need to develop a scalable Python SaaS product with Django, Flask, or FastAPI.